Overview
Telnet is a network protocol that allows for remote communication between computers. It has been widely used for decades, even though it is generally thought that noone uses it anymore due to security concerns. In January 2026, a critical vulnerability was discovered in Telnet, identified as “CVE-2026-24061”. This vulnerability allows attackers to execute arbitrary code on affected systems without any authentication. The severity of this vulnerability is rated as 9.8/10, making it a critical security risk for any system that still uses Telnet.
Background
Telnet
Telnet is a client-server application protocol that provides access to virtual terminals of remote systems on local area networks or the Internet. Its main goal was to “connect terminal devices” and terminal-oriented processes.
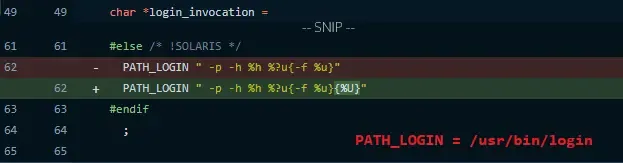
Commit from 2015
When a user uses Telnet , it must authenticate first. To authenticate, telnetd uses the login program in linux logic – /usr/bin/login, which authenticates the user and creating a session that gives them an interactive shell.
The purpose of insertion of %U in telnetd.c is to replace the value of an USER environment variable. The Telnet protocol enables the user to set of the USER environment variable, this is used to pre-fill the username used in the authentication (autologin) with login command. The -a option is used to specify that the username should be taken from the USER environment variable.
When we look at the manual of login command, we can see that it has a -f option, which allows to “skip authentication” and directly log in as the specified user. This means that if an attacker can control the value of the USER environment variable, they can potentially exploit this vulnerability to execute arbitrary code on the affected system.
Exploitation
USER='-f root' telnet -a <target_ip>This command sets the USER environment variable to ‘-f root’, which tells the login program to skip authentication and log in as the root user.
Impact and Response
The disclosure of CVE-2026-24061 triggered a chaos across the world. Exploitation began almost immediately. By January 22, mere days after disclosure, threat intelligence observed three distinct waves of attacks:
- Probing: Scanners sending minimal payloads to check for the vulnerability.
- Inline Execution: Attackers executing commands like uname -a immediately after bypassing login.
- Botnet Recruitment: “Downloader stagers” were observed attempting to pull malicious scripts (using curl or wget) to install botnet malware or miners.
CISA added CVE-2026-24061 to its Known Exploited Vulnerabilities (KEV) catalog on January 26, 2026, mandating that US federal agencies patch or disable the service by February 16.